This document provides examples about how to grant a user permissions to view and use specific resources in the TencentDB console by using a CAM policy.
Full access policy for TencentDB
To grant a user permissions to create and manage TencentDB instances, you can implement the QcloudCDBFullAccess policy for the user.
QcloudCDBFullAccess: This policy indicates full read-write access permissions to TencentDB for MySQL instances, including permissions for MySQL and related security groups, monitoring, user groups, backups, VPCs, and KMS. It is suitable for users who need to fully manage and operate TencentDB for MySQL instances.
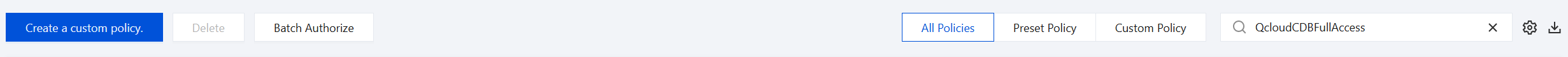
Go to the policy management interface, enter QcloudCDBFullAccess in the search box in the upper right corner, and then this policy can be found. The policy syntax is as follows:
{
"statement": [
{
"action": [
"cdb:*"
],
"effect": "allow",
"resource": "*"
},
{
"action": [
"vpc:*"
],
"effect": "allow",
"resource": "*"
},
{
"action": [
"cvm:*"
],
"effect": "allow",
"resource": "qcs::cvm:::sg/*"
},
{
"action": [
"cos:*"
],
"effect": "allow",
"resource": "*"
},
{
"action": [
"monitor:*",
"cam:ListUsersForGroup",
"cam:ListGroups",
"cam:GetGroup"
],
"effect": "allow",
"resource": "*"
},
{
"action": [
"kms:CreateKey",
"kms:GenerateDataKey",
"kms:Decrypt",
"kms:ListKey"
],
"effect": "allow",
"resource": "*"
}
],
"version": "2.0"
}
The above policy achieves its goal by allowing the user to separately authorize the use of TencentDB, VPC, security group, COS, KMS, and all resources available in the monitor with the CAM policy.
Read-only permission policy for TencentDB
To grant a user permissions to query information and data of the TencentDB for MySQL instances, but not create, delete, or modify the information and data, use the policy named QcloudCDBInnerReadOnlyAccess for the user.
QcloudCDBInnerReadOnlyAccess: This policy indicates read-only access permissions to TencentDB for MySQL instances. It is suitable for users who only need to query information and data of TencentDB for MySQL instances, but cannot perform operations such as creation, deletion, modification, or configuration changes. For example, finance or audit personnel (who need to view usage and fees of database resources but cannot modify instances).
Note:
We recommend that you configure the read-only policy for TencentDB.
You can go to the policy management interface, enter QcloudCDBInnerReadOnlyAccess in the search box in the upper right corner, and then this policy can be found. The policy syntax is as follows:
{
"statement": [
{
"action": [
"cdb:Describe*"
],
"effect": "allow",
"resource": "*"
}
],
"version": "2.0"
}
To grant a user permissions to view TencentDB instances and related resources (VPC, security groups, COS, and Cloud Monitor) but not create, delete, or modify them, you can implement the QcloudCDBReadOnlyAccess policy for the user.
QcloudCDBReadOnlyAccess: This policy indicates read-only access permissions to resources related to TencentDB for MySQL. It is suitable for users who only need to view TencentDB for MySQL instances and related resources, but cannot modify or delete these resources. For example, Ops monitoring personnel (who only need to view the database status and monitoring data, but cannot modify the configurations), and developers (who only need to query database information but cannot modify the instance configurations).
Go to the policy management interface, enter QcloudCDBReadOnlyAccess in the search box in the upper right corner, and then this policy can be found. The policy syntax is as follows:
{
"statement": [
{
"action": [
"cdb:Describe*"
],
"effect": "allow",
"resource": "*"
},
{
"action": [
"monitor:Describe*",
"monitor:Get*",
"cam:ListUsersForGroup",
"cam:ListGroups",
"cam:GetGroup"
],
"effect": "allow",
"resource": "*"
}
],
"version": "2.0"
}
The above policy achieves its goal by allowing the user to separately authorize the use of the following operations with the CAM policy.
All operations in TencentDB that begin with "Describe".
All operations in VPC that begin with "Describe", "Inquiry", or "Get".
All operations in the security group that begin with the word DescribeSecurityGroup.
All operations in COS that begin with "List", "Get", and "Head" as well as the "OptionsObject" operation.
All operations in the monitor.
Policy for granting a user permissions to use APIs not at the resource level
To grant a user permissions to use only APIs not at the resource level, you can implement the QcloudCDBProjectToUser policy for the user.
QcloudCDBProjectToUser: This policy indicates project permissions for sub-accounts of TencentDB for MySQL. It is suitable for users who require access to and operation permissions for non-resource-level APIs. This policy is suitable for testers. Go to the policy management interface, enter QcloudCDBProjectToUser in the search box in the upper right corner, and then this policy can be found. The policy syntax is as follows:
{
"version": "2.0",
"statement": [
{
"action": [
"cdb:BalanceRoGroupLoad",
"cdb:CancelBatchOperation",
"cdb:CreateBatchJobFiles",
"cdb:CreateDBInstance",
"cdb:CreateDBInstanceHour",
"cdb:CreateMonitorTemplate",
"cdb:CreateParamTemplate",
"cdb:DeleteBatchJobFiles",
"cdb:DeleteMonitorTemplate",
"cdb:DeleteParamTemplate",
"cdb:DescribeBatchJobFileContent",
"cdb:DescribeBatchJobFiles",
"cdb:DescribeBatchJobInfo",
"cdb:DescribeProjectSecurityGroups",
"cdb:DescribeDefaultParams",
"cdb:DescribeMonitorTemplate",
"cdb:DescribeParamTemplateInfo",
"cdb:DescribeParamTemplates",
"cdb:DescribeRequestResult",
"cdb:DescribeRoGroupInfo",
"cdb:DescribeRoMinScale",
"cdb:DescribeTasks",
"cdb:DescribeUploadedFiles",
"cdb:ModifyMonitorTemplate",
"cdb:ModifyParamTemplate",
"cdb:ModifyRoGroupInfo",
"cdb:ModifyRoGroupVipVport",
"cdb:StopDBImportJob",
"cdb:UploadSqlFiles"
],
"effect": "allow",
"resource": "*"
}
]
}
Policy for granting a user permissions to manipulate a specific TencentDB instance
If you want to grant a user operation permissions for a specific TencentDB for MySQL instance, you can associate the following policy with the user. The following policy allows the user to have operation permissions for the TencentDB for MySQL instances with ID cdb-xxx in the Guangzhou region.
{
"version": "2.0",
"statement": [
{
"action": "cdb:*",
"resource": "qcs::cdb:ap-guangzhou::instanceId/cdb-xxx",
"effect": "allow"
}
]
}
Policy for granting a user permissions to manipulate TencentDB instances in batches
If you want to grant a user operation permissions for batch TencentDB for MySQL instances, you can associate the following policy with the user. The following policy allows the user to have operation permissions for the TencentDB for MySQL instances with IDs cdb-xxx and cdb-yyy in the Guangzhou region, and the instances with ID cdb-zzz in the Beijing region.
{
"version": "2.0",
"statement": [
{
"action": "cdb:*",
"resource": ["qcs::cdb:ap-guangzhou::instanceId/cdb-xxx", "qcs::cdb:ap-guangzhou::instanceId/cdb-yyy", "qcs::cdb:ap-beijing::instanceId/cdb-zzz"],
"effect": "allow"
}
]
}
Policy for granting a user permissions to manipulate TencentDB instances in a specific region
If you want to grant a user operation permissions for the TencentDB for MySQL instances of a specific region, you can associate the following policy with the user. The following policy allows the user to have operation permissions for the TencentDB for MySQL machines in the Guangzhou region.
{
"version": "2.0",
"statement": [
{
"action": "cdb:*",
"resource": "qcs::cdb:ap-guangzhou::*",
"effect": "allow"
}
]
}
Custom policy
If preset policies cannot meet your requirements, you can create custom policies as shown below. If permissions are granted by resources, for a TencentDB API operation that does not support authorization at the resource level, you can still authorize a user to perform it, but you must specify * as the resource element in the policy statement.
The syntax of custom policies is as follows:
{
"version": "2.0",
"statement": [
{
"action": [
"Action"
],
"resource": "Resource",
"effect": "Effect"
}
]
}
Replace "Action" with the operation to be allowed or denied.
Replace "Resource" with the resources that you want to authorize the user to manipulate.
Replace "Effect" with "Allow" or "Deny".
Documentation
For the definition of Cloud Access Management (CAM), see CAM Overview.