通过 iframe 内嵌 CLS(旧方案)
下载
聚焦模式
字号
适用场景
在外部系统服务中(例如公司内部运维或运营系统)快速集成日志服务的查询分析能力。
无需管理众多腾讯云子账号,方便将日志数据分享给他人进行查看。
使用演示代码实现免登录
操作步骤
1. 打开 访问管理 CAM 页面,创建 CAM 角色,选择角色载体为腾讯云账号,并允许登录控制台,并为 CAM 角色配置相应的访问权限,例如只读策略权限
QcloudCLSReadOnlyAccess ,并命名为 CLSReadOnly 。复制策略的 RoleArn 信息。2. 打开 访问管理策略 页面,新建自定义策略,选择按策略生成器创建。进入页面后选择JSON标签,在策略内容中填写以下内容,注意将${YOUR_UIN}替换为账号的Uin(Resource 内容为创建的角色的 RoleArn ,如果策略名不一致,请注意修改)。点击下一步,并设置访问策略名为
PlayClsPolicy 。{"version": "2.0","statement": [{"effect": "allow","action": ["sts:AssumeRole"],"resource": ["qcs::cam::uin/${YOUR_UIN}:roleName/CLSReadOnly"]}]}
3. 打开 新建用户 页面,选择自定义创建。类型设置为可访问资源并接受消息,用户名可设置为 PlayClsUser ,访问方式为编程访问,用户权限设置为上步骤新建的策略
PlayClsPolicy 。提交新建用户操作后,复制保留生成的密钥 SecretId 和 SecretKey 。4. 克隆免密登录控制台演示项目代码 cls-iframe-demo 。参考项目ReadMe内容,在根目录创建
.env 文件,填写 RoleArn、SecretId、SecretKey 信息,即完成了必要参数值的填写。注意:
代码泄漏可能会导致 SecretId 与 SecretKey 泄漏,从而影响账号安全。为了保证账号安全,可参考云 API 密钥安全方案推荐,安全使用密钥。同时根据权限最小化原则,使用具备最小化权限的子账户密钥。
参考免密登录控制台演示程序的 ReadMe文档,运行项目后,即可查看免密登录控制台效果。
注意:
该示例中不包含鉴权外部系统鉴权逻辑,部署后所有访问者(即使未登录腾讯云)均可以在示例中配置的角色权限查看账户中的数据。为保障数据隐私及安全,请自行添加外部系统鉴权逻辑或限制其仅在内网中可访问,以确保有权限的用户才能够查看该页面。
5. 拼接日志服务免登录目标地址
s_url(可选,获取后填写在免登录项目的配置文件中,访问免登录服务后将自动跳转到此地址)日志服务检索分析页面基础地址:
https://console.tencentcloud.com/cls/search?region=<region>&topic_id=<topic_id>
日志服务检索分析页面 URL 参数说明:
参数名称 | 必填 | 类型 | 描述 |
region | 是 | String | 地域简称,例如:ap-shanghai 表示上海地域,其它可用地域简称参见 可用地域 |
topic_id | 否 | String | 日志主题 ID |
logset_name | 否 | String | 日志集名称 |
topic_name | 否 | String | 日志主题名称 |
time | 否 | String | 要检索日志的起始时间至结束时间,格式样例:2021-07-15T10:00:00.000,2021-07-15T12:30:00.000 |
queryBase64 | 否 | String | 检索分析语句,采用 base64Url 编码 |
hideWidget | 否 | Boolean | 隐藏右下角客服/文档按钮:默认不隐藏,true 表示隐藏 |
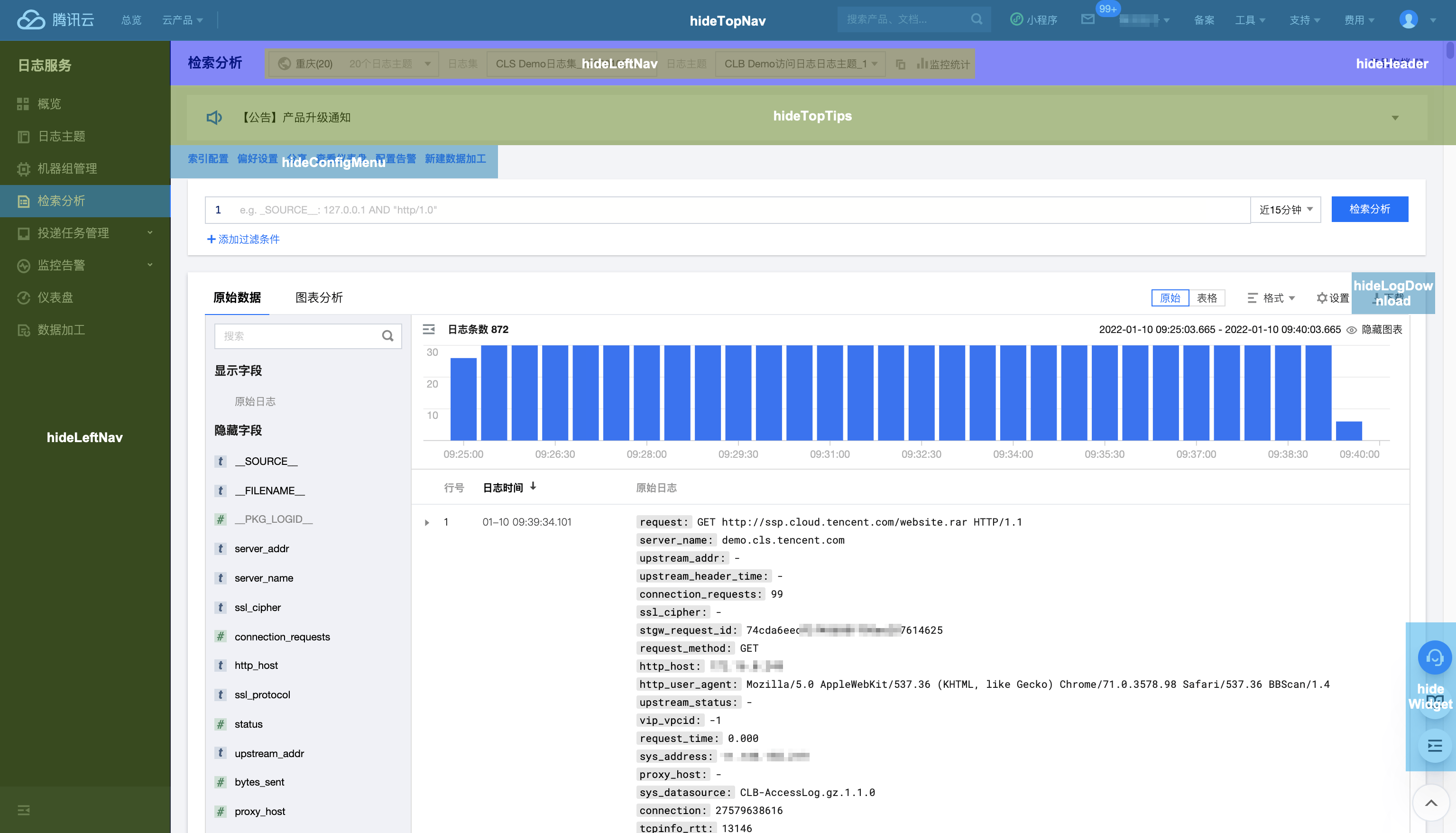
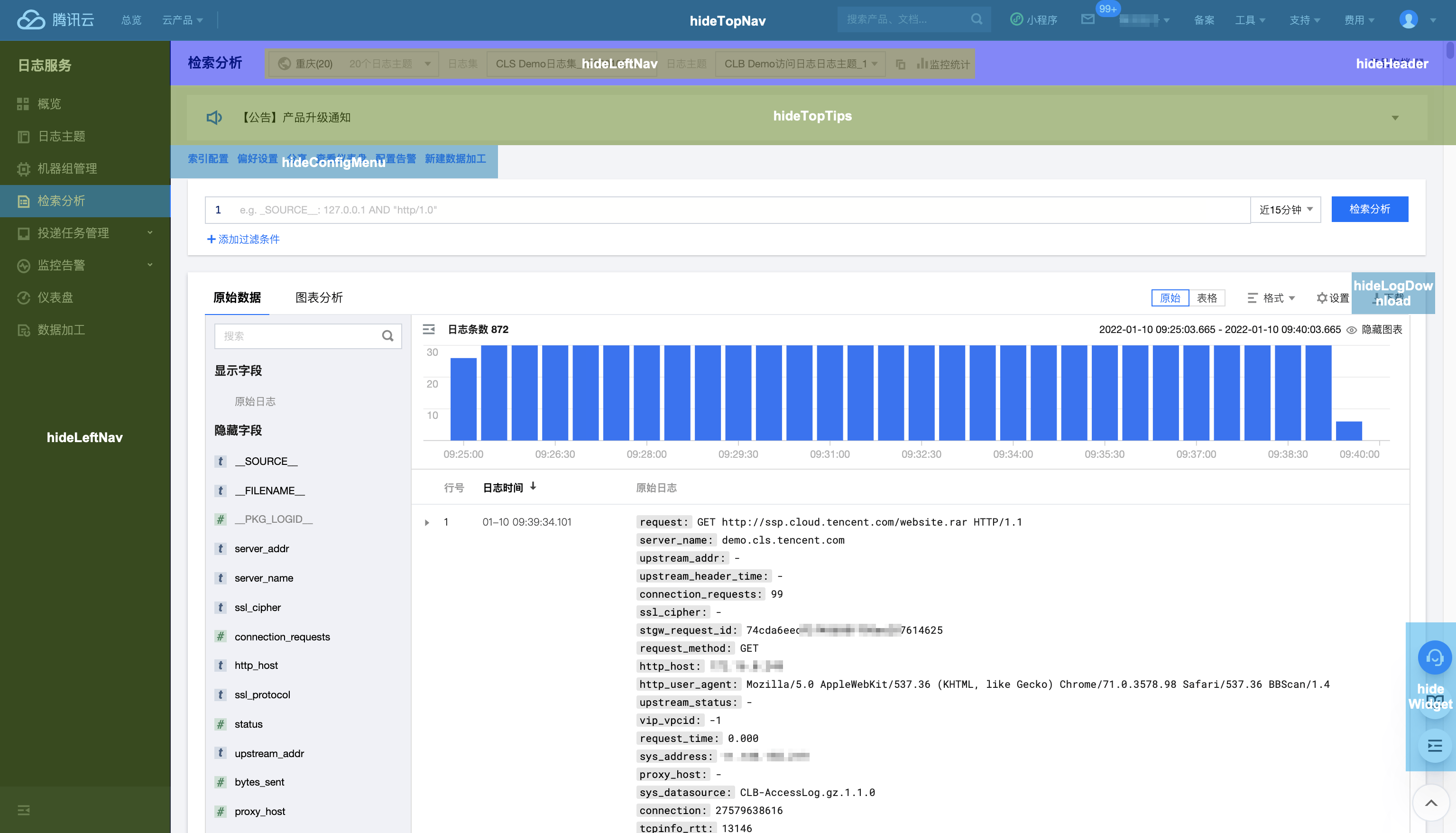
hideTopNav | 否 | Boolean | 隐藏腾讯云控制台顶部菜单:默认不隐藏,true 表示隐藏 |
hideLeftNav | 否 | Boolean | 隐藏腾讯云控制台左侧菜单:默认不隐藏,true 表示隐藏 |
hideTopicSelect | 否 | Boolean | 隐藏日志主题选择控件(包括地域、日志集和日志主题):默认不隐藏,true 表示隐藏 |
hideHeader | 否 | Boolean | 隐藏日志主题选择控件及所在行:默认不隐藏,true 表示隐藏,尽在 hideTopicSelect 为 true 时生效 |
hideTopTips | 否 | Boolean | 隐藏顶部产品公告提示:默认不隐藏,true 表示隐藏 |
hideConfigMenu | 否 | Boolean | 隐藏日志主题配置管理菜单:默认不隐藏,true 表示隐藏 |
hideLogDownload | 否 | Boolean | 隐藏原始日志下载按钮:默认不隐藏,true 表示隐藏 |
注意:
可通过两种方式在 URL 参数中指定需要检索的日志主题:
topic_id:根据日志主题 ID 指定日志主题。
logset_name+topic_name:根据日志集名称及日志主题名称指定日志主题,需要注意的是当日志集或日志主题名称发生变化时,采用该方式的 URL 会失效。
如 topic_id、logset_name 和 topic_name 参数同时存在,将以 topic_id 为准。
隐藏参数与页面模块对应关系:
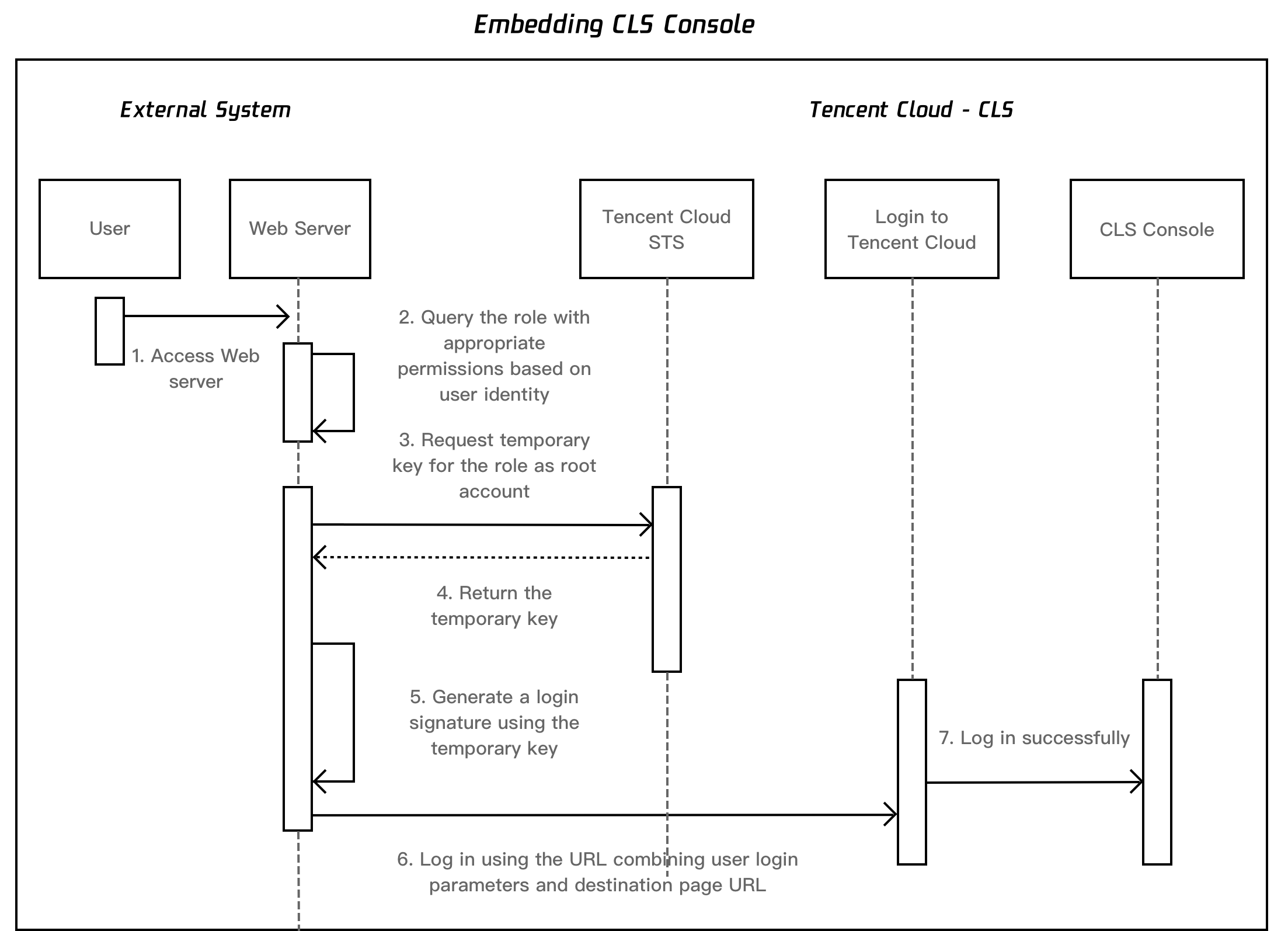
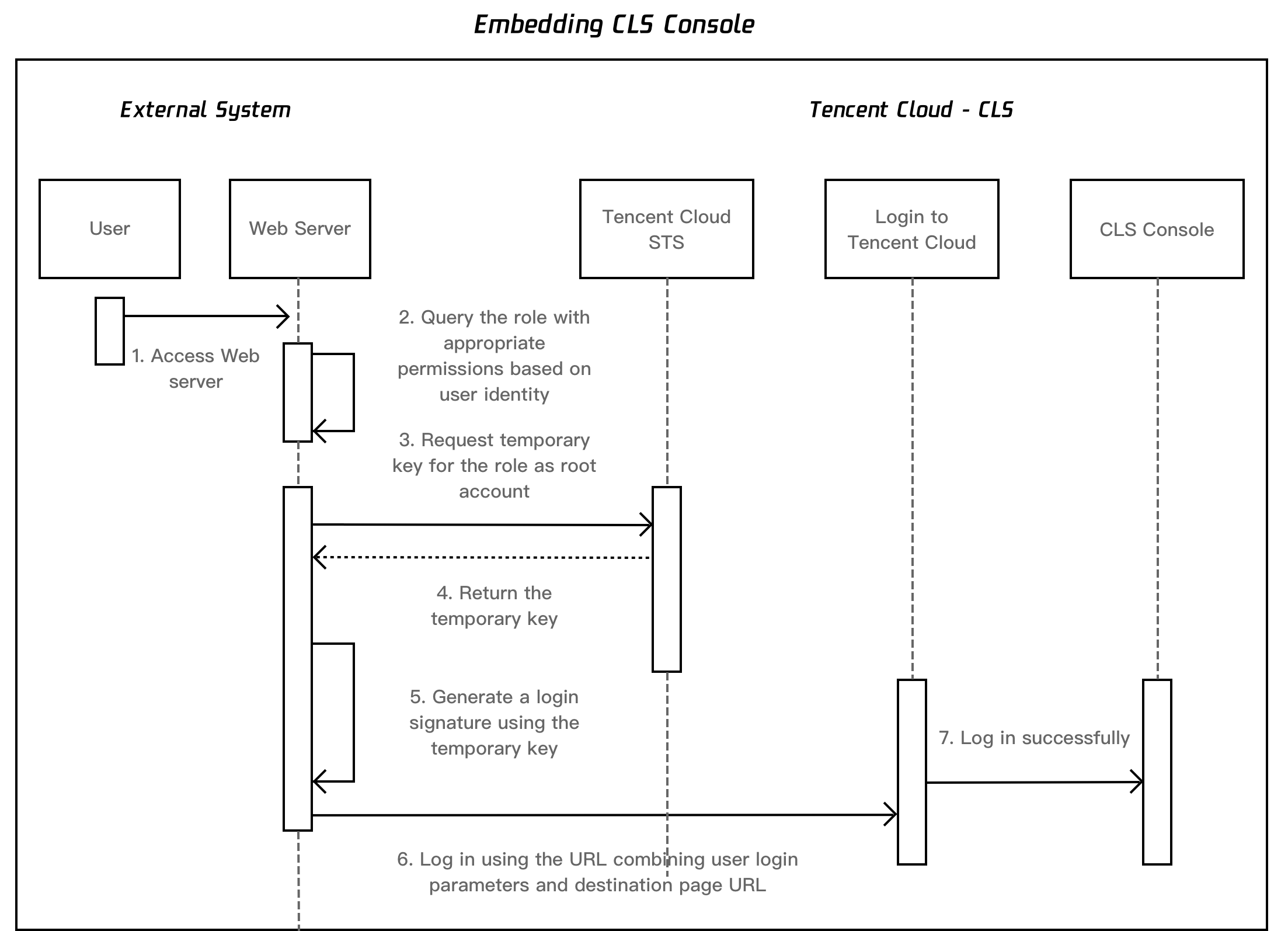
自行开发实现免登录
操作步骤
注意:
代码泄漏可能会导致 SecretId 与 SecretKey 泄漏,从而影响账号安全。为了保证账号安全,可参考云 API 密钥安全方案推荐,安全使用密钥。同时根据权限最小化原则,使用具备最小化权限的子账户密钥。
1. 参考使用演示代码实现免登录中的内容,在腾讯云账号中配置相应的
CLS 只读角色、扮演角色的自定义策略、绑定自定义策略的子账号。配置完成后保存对应的 RoleArn、SecretId、SecretKey 信息。2. 参考使用演示代码实现免登录中的内容,根据自身诉求,获取日志服务免登录目标地址
s_url。 3. 在每次需要打开免登录访问页面时,重复以下步骤内容。
4. 使用获取到的密钥,调用 STS AssumeRole 接口,申请扮演角色的临时密钥。
5. 基于获取到的临时密钥,生成登录签名信息。
5.1 签名参数排序。
对要求签名的参数按照字母表或数字表递增顺序的排序,先考虑第一个字母,在相同的情况下考虑第二个字母,依此类推。您可以借助编程语言中的相关排序函数来实现这一功能,例如 PHP中 的 ksort 函数。其中签名参数包含以下内容:
参数名称 | 必选 | 类型 | 描述 |
action | 是 | String | 操作动作,固定为 roleLogin |
timestamp | 是 | Int | 当前时间戳 |
nonce | 是 | Int | 随机整数,取值10000-100000000 |
secretId | 是 | String | STS 返回的临时 AK |
5.2 拼接参数。
将上一步排序好的请求参数,按“参数名称=参数值”拼接,例如:
action=roleLogin&nonce=67439&secretId=AKI***PLE×tamp=1484793352
5.3 拼接签名串。
按请求方法 + 请求主机 +请求路径 + ? + 请求字符串的规则拼接签名串。
参数 | 必选 | 描述 |
请求主机和路径 | 是 | 固定为www.tencentcloud.com/login/roleAccessCallback |
请求方法 | 是 | 支持 GET 或 POST |
签名串示例
GETwww.tencentcloud.com/login/roleAccessCallback?action=roleLogin&nonce=67439&secretId=AKI***PLE×tamp=1484793352
5.4 生成签名串。
使用 HMAC-SHA1算法对字符串签名,目前支持 HMAC-SHA1 和 HMAC-SHA256。具体代码如下,以 PHP 语言为例:
$secretKey = 'Gu5***1qA';$srcStr = 'GETwww.tencentcloud.com/login/roleAccessCallback?action=roleLogin&nonce=67439&secretId=×tamp=1484793352';$signStr = base64_encode(hash_hmac('sha1', $srcStr, $secretKey, true));echo $signStr;
PHP 版本示例代码
$secretId = "AKI***"; //STS 返回的临时 AK$secretKey = "Gu5***PLE"; //STS 返回的临时 Secret$token = "ADE***fds"; //STS 返回的安全 TOKEN$param["nonce"] = 11886; //rand(10000,100000000);$param["timestamp"] = 1465185768; //time();$param["secretId"] = $secretId;$param["action"] = "roleLogin";ksort($param);$signStr = "GETwww.tencentcloud.com/login/roleAccessCallback?";foreach ( $param as $key => $value ) {$signStr = $signStr . $key . "=" . $value . "&";}$signStr = substr($signStr, 0, -1);$signature = base64_encode(hash_hmac("sha1", $signStr, $secretKey, true));echo $signature.PHP_EOL;
6. 拼接完整登录信息以及目的页面地址进行登录。
参数值需要 urlencode 编码
https://www.tencentcloud.com/login/roleAccessCallback?algorithm=<签名时加密算法,目前只支持 sha1和 sha256,不填默认 sha1>&secretId=<签名时 secretId>&token=<临时密钥 token>&nonce=<签名时 nonce>×tamp=<签名时 timestamp>&signature=<签名串>&s_url=<登录后目的 URL>
7. 使用生成的最终链接,访问腾讯云日志服务控制台页面。例如检索分析页面的内嵌访问链接如下:
https://www.tencentcloud.com/login/roleAccessCallback?nonce=52055817&s_url=https%3A%2F%2Fconsole.tencentcloud.com%2Fcls%2Fsearch%3Fregion%3Dap-guangzhou%26start_time%3D2020-05-26%25252014%25253A01%25253A18%26end_time%3D2020-05-26%25252014%25253A16%25253A18&secretId=AKID-vHJ7WPHcy_RVIOm-QTIktXOf9S9z_k_JackOp3dyQPJwmDrNLQJuiNuw9******&signature=eXeWaDn6iJlcPp1sqqGd6m9%2FQk****×tamp=1592455018&token=5e4vuBHL7fBQPi1V9fvSINw4Vu7PSr9Ic3de78b86109c171eb4e3ea27c137c1fIWKU8JC-LO01L87sIYlfTSaHHXeHcqim7Jg9hBuN2nbdfgeBUPXhmpyAk4G6e9bHFZ-7yNRig7Y33CQHxh6jOesP4VfhRzQprWGRtC5No1ty******-aoj_WJhA55oyvqaqxw2jtTdh8nx9OjJr3tlbIa9oJe7aZYoPbdpFqrF6ZjlCPPap2yQB_SkUsWwDl_9BrK2Km3U2IocdvQ7QxrW0ts1aiBi7xtTSJRcfkBYPYEV_YoJrtkhYW3E4L47imA1bfVAjM9F5uKWzVzsDGDT0aCUU9mqdb4vjJrY8tm-wJKKEe8eiyY9EbkH3VWnFV2YocYNDJqFyjKOWR******
技术实现原理
登录原理流程图:
文档反馈