CLB로 리얼 서버의 클라이언트 실제 IP 획득
다운로드
포커스 모드
폰트 크기
CLB로 클라이언트 실제 IP 획득 설명
CLB의 4계층 리스너(TCP/UDP/TCP SSL/QUIC)는 별도의 설정 없이 리얼 서버가 클라이언트의 실제 IP를 직접 획득할 수 있도록 지원합니다. 기본 설정에서는 리얼 서버가 획득한 소스 IP가 곧 클라이언트의 실제 IP입니다.
하지만, CLB와 리얼 서버 사이에 하나 이상의 NAT 게이트웨이가 존재하는 경우, 리얼 서버는 클라이언트의 실제 소스 IP를 획득할 수 없습니다. 이러한 상황에서는 CLB의 4계층 리스너에서 Proxy Protocol을 활성화할 수 있으며, Proxy Protocol을 통해 클라이언트의 실제 소스 IP를 리얼 서버로 전달할 수 있습니다.
주의:
이 기능을 사용하려면 리얼 서버 또한 Proxy Protocol을 활성화해야 하며, 그래야만 클라이언트의 실제 IP 주소를 획득할 수 있습니다. 리얼 서버가 Proxy Protocol을 분석할 수 없는 경우 Proxy Protocol 설정을 활성화하면 서비스 이상이 발생할 수 있습니다.
해당 기능은 온라인 무중단 전환을 지원하지 않으며, Proxy Protocol로 전환 시에는 서비스 중단 후 업그레이드가 필요하므로 신중히 설정하십시오.
CLB는 Proxy Protocol v2만 지원합니다. Proxy Protocol v2는 TCP 및 UDP 등 다양한 전송 프로토콜을 지원합니다. 자세한 내용은 The PROXY protocol을 참조하십시오.
해당 기능은 표준 계정 유형에서만 지원되며, 기존 계정 유형은 지원하지 않습니다. 계정 유형 확인 방법은 계정 유형 판단을 참조하십시오.
IPv4 및 IPv6 인스턴스의 TCP/UDP/TCP SSL/QUIC 리스너에서만 해당 기능을 지원합니다.
IPv6 CLB의 TCP/UDP 리스너에서 Proxy Protocol 설정 기능은 현재 내부 테스트 중이며, 필요한 경우 티켓 제출을 통해 신청해 주세요.
Proxy Protocol 설명
Proxy Protocol을 활성화하면 프록시 서버가 요청을 리얼 서버로 포워딩할 때 클라이언트의 원래 네트워크 연결 정보를 요청 헤더에 포함시켜 전송합니다. 리얼 서버는 Proxy Protocol 헤더를 분석하여 클라이언트의 실제 IP 주소, 포트, 전송 프로토콜 등의 정보를 획득할 수 있습니다.
Proxy Protocol을 통해 리얼 서버는 클라이언트의 원래 네트워크 연결 정보를 정확히 획득할 수 있어 보다 정밀한 로그 기록, 접근 제어, 트래픽 모니터링 등의 작업이 가능합니다.
Proxy Protocol V2
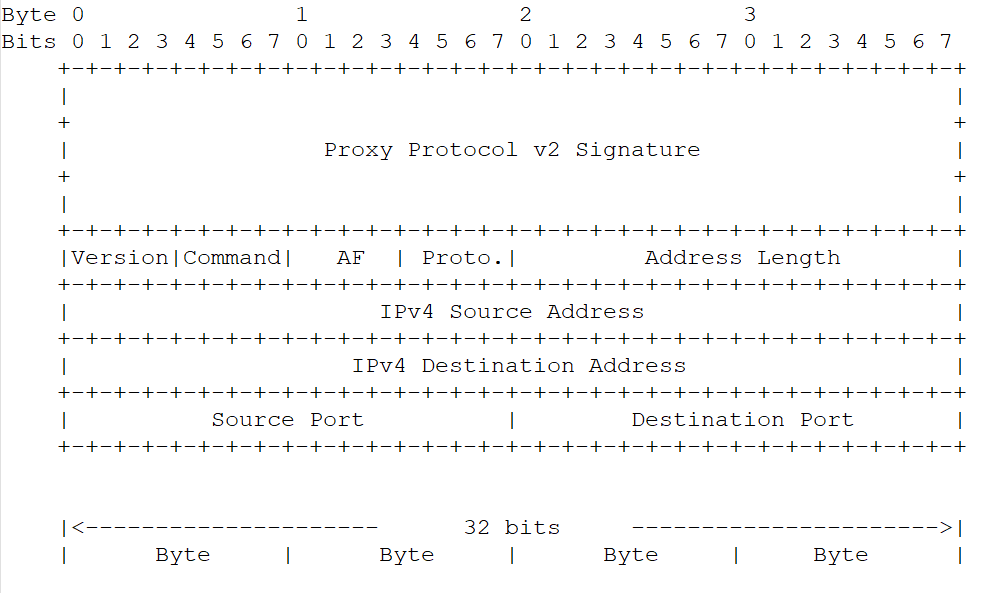
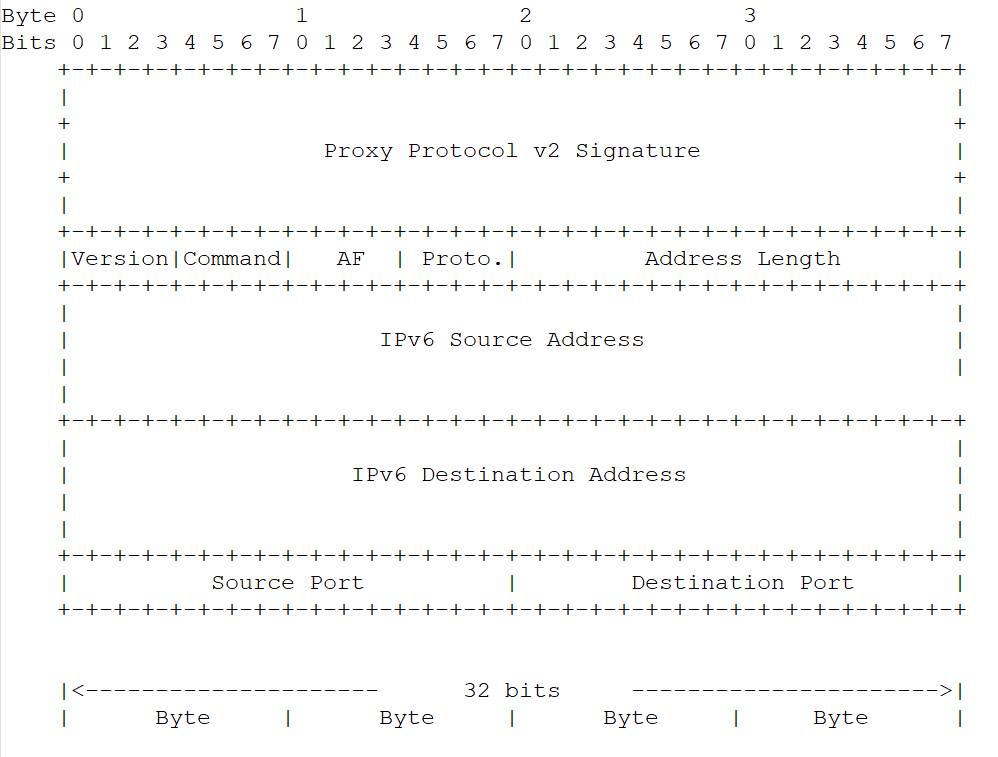
Proxy Protocol V2는 바이너리 형식을 사용하며 TCPv4, TCPv6, UDPv4, UDPv6 프로토콜을 지원합니다. 형식은 다음과 같습니다.
IPv4 형식
IPv6 형식
전제 조건
Proxy Protocol을 활성화하기 전, 리얼 서버가 Proxy Protocol v2를 지원하는지 반드시 확인해야 합니다. 그렇지 않으면 새로운 연결이 실패할 수 있습니다.
본 문서는 IPv4 CLB의 TCP 리스너를 예시로 설명합니다.
작업 절차
절차 1: TCP 리스너에서 Proxy Protocol 설정 활성화
1. CLB 콘솔에 로그인한 후, 왼쪽 네비게이션 바에서 인스턴스 관리를 클릭합니다.
2. CLB 인스턴스 목록 페이지 왼쪽 상단에서 리전을 선택한 후, 인스턴스 목록 오른쪽의 작업 열에서 리스너 설정을 클릭합니다.
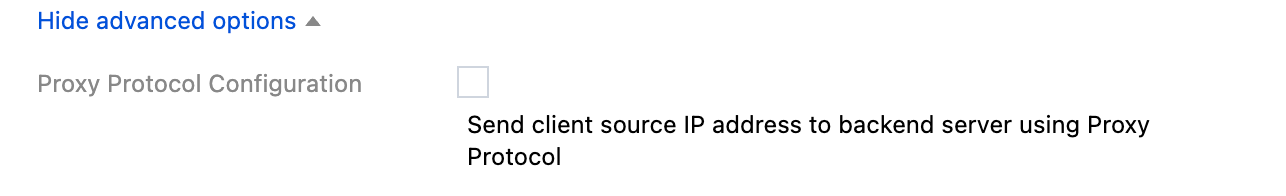
3. TCP/UDP/TCP SSL/QUIC 리스너 목록에서 대상 리스너 상세 정보를 클릭하여 ProxyProtocol 설정이 활성화됨인지 확인합니다. 활성화되지 않은 경우, 리스너를 편집하고 고급 옵션에서 ProxyProtocol 설정을 선택한 후 저장합니다.
절차 2: 리얼 서버에서 Proxy Protocol 활성화
다음은 CentOS 7.9 운영체제와 Nginx 1.20.1 버전을 기준으로 한 설정 예시입니다. 사용 환경에 따라 적절히 조정해 주세요.
1. 리얼 서버에 로그인한 후, nginx -t 명령을 실행하여 설정 파일 경로를 확인합니다. 기본 경로는 /etc/nginx/nginx.conf이며, 사용 환경에 따라 다를 수 있습니다.
2. 설정 파일에서 Proxy Protocol 관련 항목을 수정하고 저장합니다. 수정 항목 예시는 다음과 같습니다.
http {# $proxy_protocol_addr 변수 설정, 클라이언트 실제 IP 기록log_format main '$proxy_protocol_addr - $remote_addr- $remote_user [$time_local] "$request" ''$status $body_bytes_sent "$http_referer" ''"$http_user_agent" "$http_x_forwarded_for"';# 리스너 포트 80 예시, proxy_protocol 키워드 추가server { listen 80 proxy_protocol;#...}}
3. sudo nginx -s reload 명령을 실행하여 Nginx 설정 파일을 다시 로드합니다.
절차 3: 리얼 서버는 클라이언트 실제 IP 획득 여부 확인
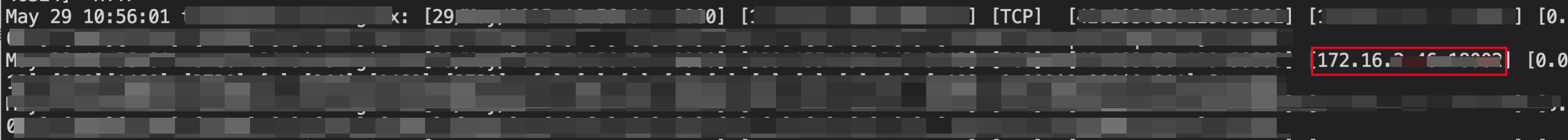
리얼 서버가 Nginx일 경우, Nginx 로그를 통해 클라이언트의 실제 IP가 제대로 획득되었는지 확인할 수 있습니다.
Nginx 로그 파일 기본 경로: /var/log/nginx/access.log
각 로그 라인의 $proxy_protocol_addr 값이 클라이언트의 실제 IP입니다.
피드백