流量采集范围配置
下载
聚焦模式
字号
功能概述
通过支持用户自定义流量采集范围,实现指定资产的流量接入全流量检测与响应(NDR)分析。用户可在 NDR 开关页面为资产实例启用 NDR 服务时,新建并配置采集范围规则。配置完成后启用服务,即可对指定资产流量进行旁路镜像,并开展 NDR 分析。
操作步骤
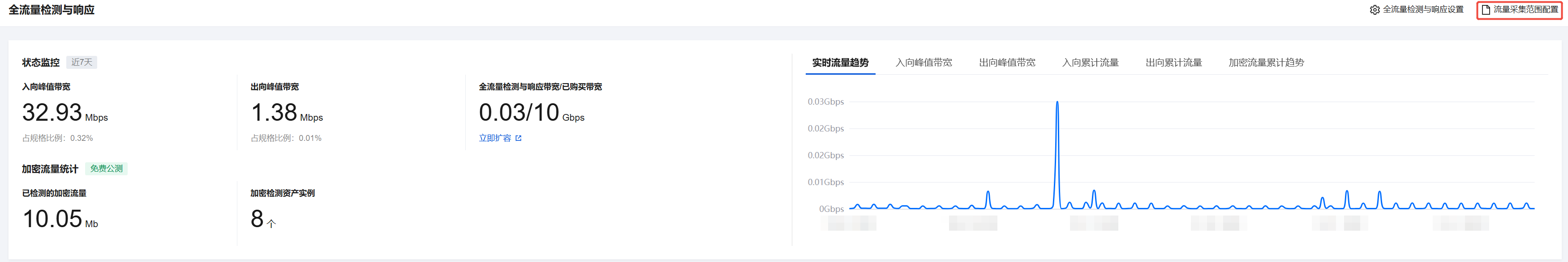
1. 登录 云防火墙控制台,在左侧导航栏中,单击全流量检测与响应(NDR)。
2. 在全流量检测与响应(NDR)页面,查看资产是否应用采集范围规则。
CVM
未配置流量采集范围时,默认采集所有出/入向的镜像流量。
已配置流量采集范围时,流量采集范围按优先级顺序从1开始进行流量匹配,即列表顶端策略最先匹配;列表底端策略最后匹配。若未匹配任何策略,则默认按不采集处理。

容器集群
开启某个全流量检测与响应开关后,该节点的所有流量将经过防火墙,进行文件解析还原,并记录流量日志。
关闭某个全流量检测与响应开关后,该节点的所有流量不会经过防火墙,不进行文件解析还原,不再记录流量日志。

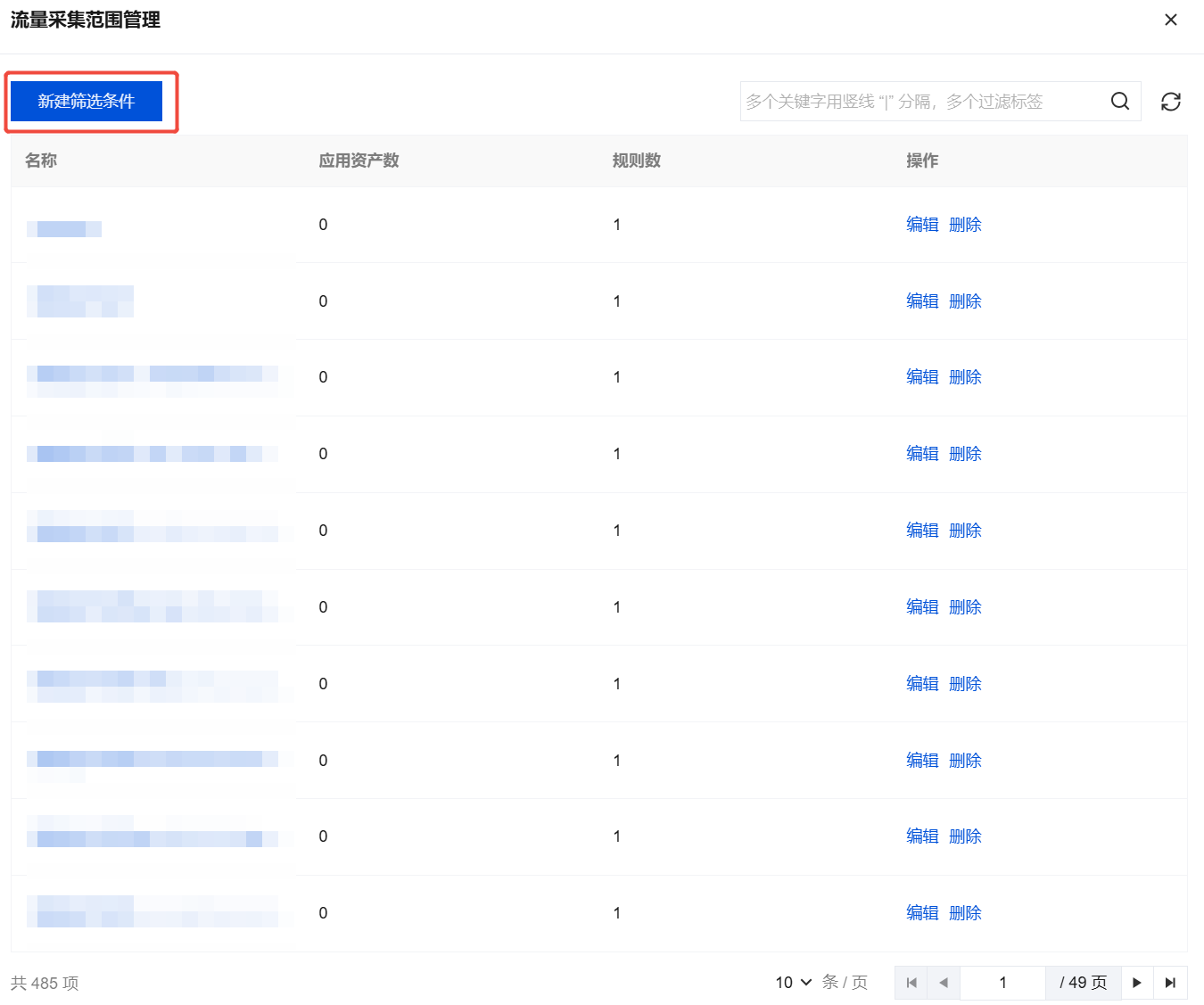
3. 在全流量检测与响应(NDR)页面,单击流量采集范围配置,查看已有筛选条件。
4. 在流量采集范围配置页面,单击新建筛选条件。
5. 在编辑筛选条件中,配置流量采集范围规则。
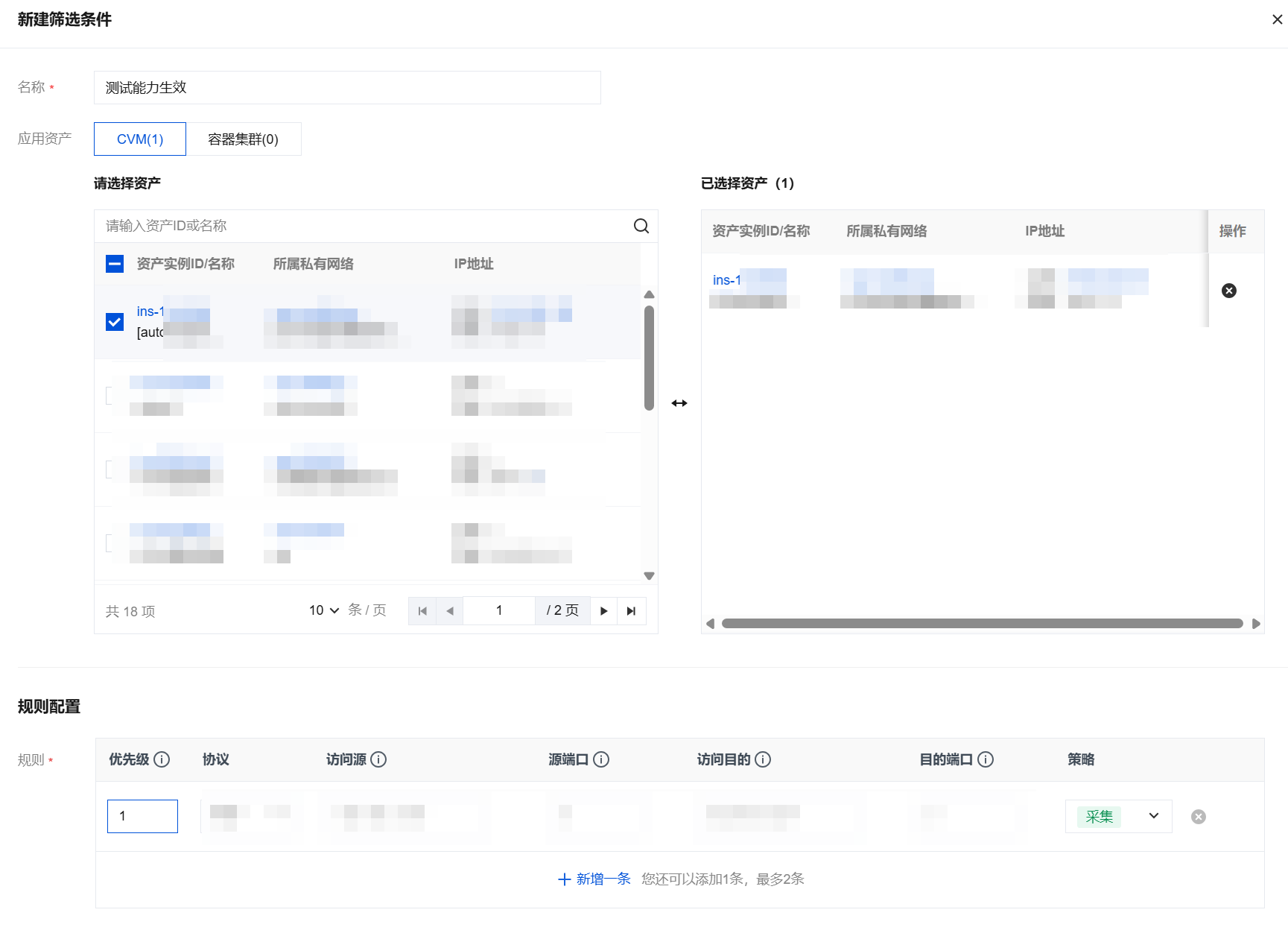
参数名称 | 参数说明 | |
基本信息 | 名称 | 规则名称。 |
| 应用资产 | 支持容器集群与 CVM。 |
规则配置 | 优先级 | 数字越小优先级越高(优先匹配),命中后执行采集策略。 |
| 协议 | 支持 TCP、UDP、ICMP 协议。 |
| 访问源 | 请用斜杠分隔 IP 与掩码,如:10.0.0.0/16。 |
| 源端口 | 源端口范围为0-65535。 支持单端口值,例如22。 支持端口范围,例如:80-88。 |
| 访问目的 | 用斜杠分隔IP与掩码,如:10.0.0.0/16。 |
| 目的端口 | 目的端口范围为0-65535。 支持单端口值,例如22。 支持端口范围,例如:80-88。 |
| 策略 | “采集”,命中五元组规则的流量接入全流量检测与响应(NDR)分析。 |
6. 单击确定,在资产列表查看应用的采集规则。

文档反馈