Release Notes
Security Announcement
Announcements
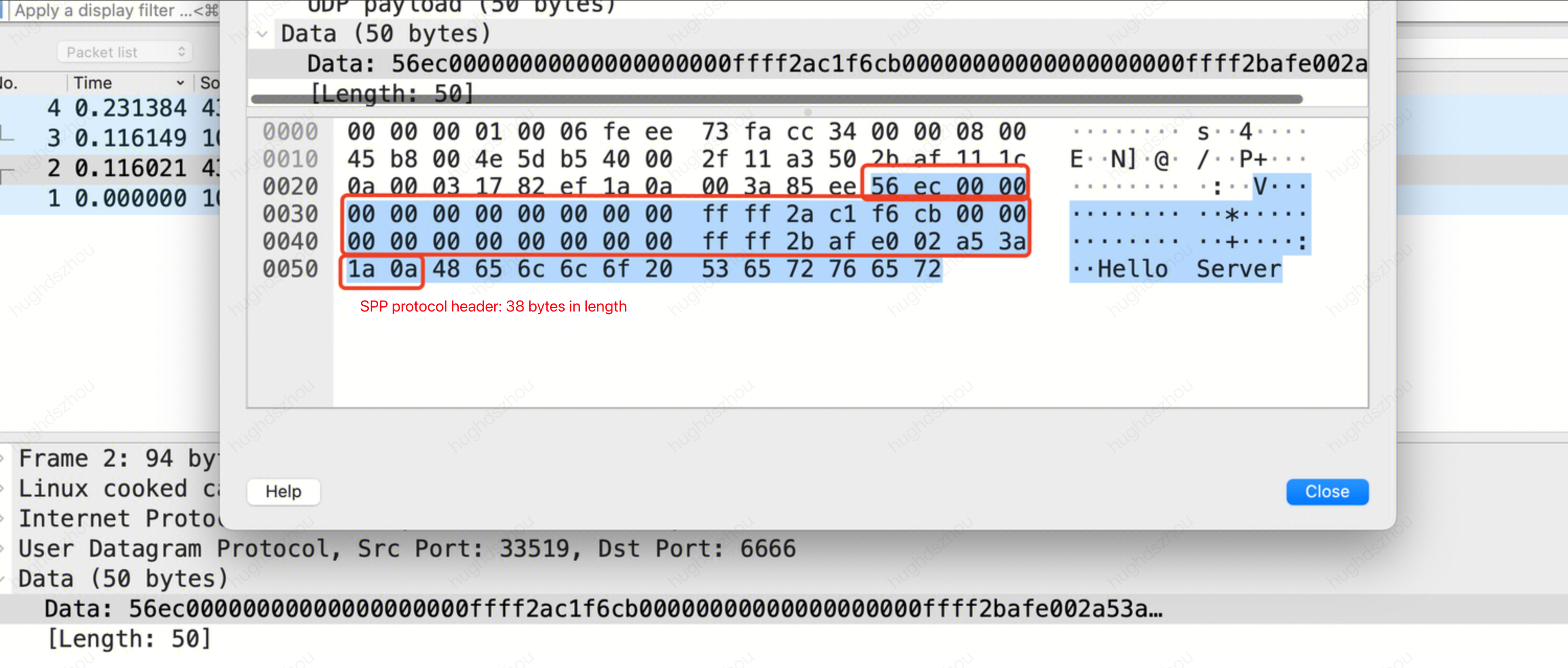
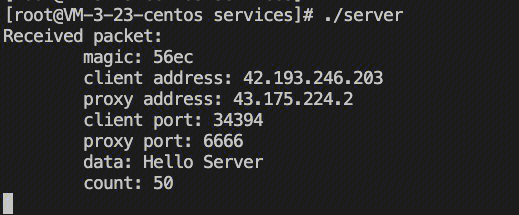
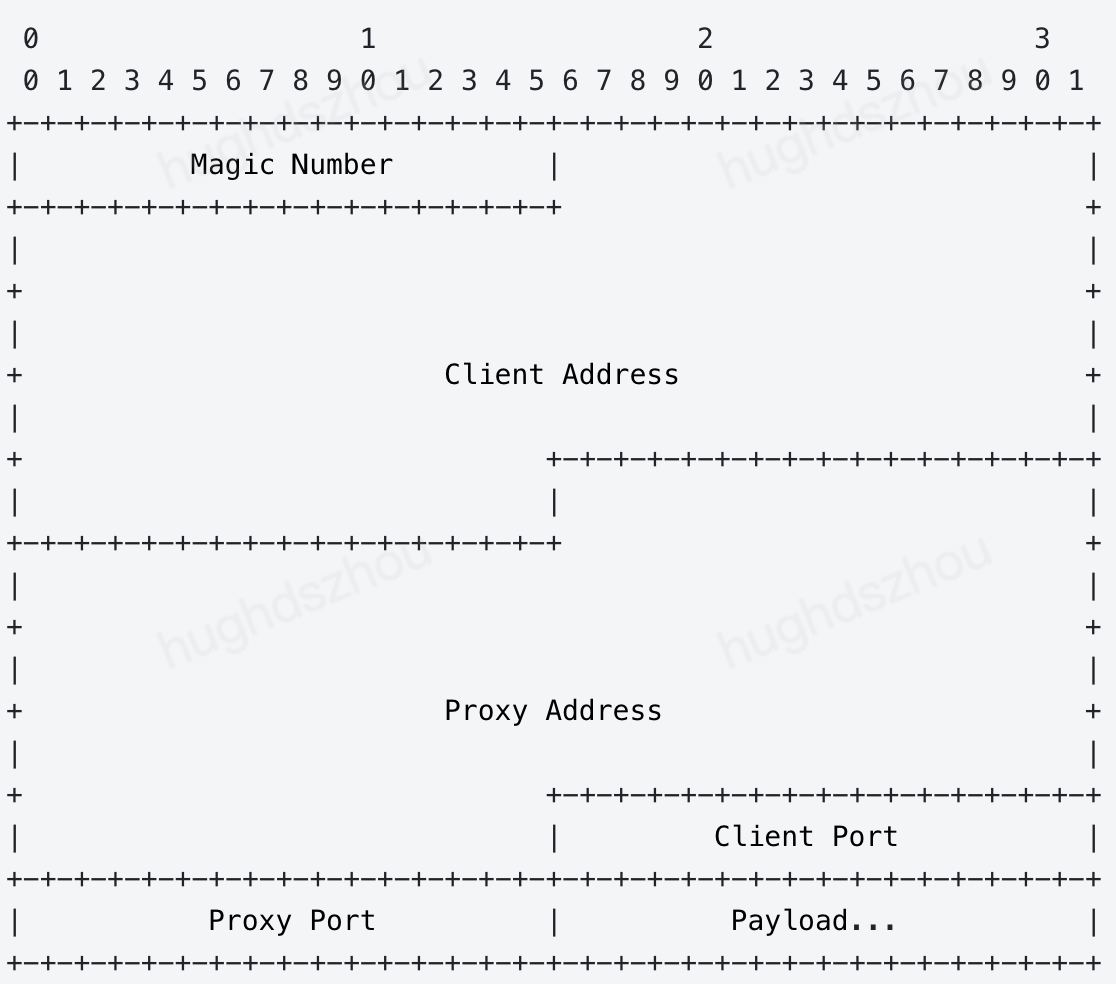
package mainimport ("encoding/binary""fmt""net")type NetworkConnection struct {Magic uint16ClientAddr net.IPProxyAddr net.IPClientPort uint16ProxyPort uint16}func handleConn(conn *net.UDPConn) {buf := make([]byte, 1024) // Create a buffer.n, addr, err := conn.ReadFromUDP(buf) // Read the data packet from the connection.if err != nil {fmt.Println("Error reading from UDP connection:", err)return}// Convert the received bytes to a NetworkConnection struct.nc := NetworkConnection{Magic: binary.BigEndian.Uint16(buf[0:2]),ClientAddr: make(net.IP, net.IPv6len),ProxyAddr: make(net.IP, net.IPv6len),}if nc.Magic == 0x56EC {copy(nc.ClientAddr, buf[2:18])copy(nc.ProxyAddr, buf[18:34])nc.ClientPort = binary.BigEndian.Uint16(buf[34:36])nc.ProxyPort = binary.BigEndian.Uint16(buf[36:38])// Print the SPP header information, including magic, real client IP and port, as well as proxy IP and port.fmt.Printf("Received packet:\\n")fmt.Printf("\\tmagic: %x\\n", nc.Magic)fmt.Printf("\\tclient address: %s\\n", nc.ClientAddr.String())fmt.Printf("\\tproxy address: %s\\n", nc.ProxyAddr.String())fmt.Printf("\\tclient port: %d\\n", nc.ClientPort)fmt.Printf("\\tproxy port: %d\\n", nc.ProxyPort)// Print the actual and effective payload.fmt.Printf("\\tdata: %v\\n\\tcount: %v\\n", string(buf[38:n]), n)} else {// Print the actual and effective payload.fmt.Printf("\\tdata: %v\\n\\tcount: %v\\n", string(buf[0:n]), n)}// Respond with a packet. Note: The 38-byte SPP header must be returned completely.response := make([]byte, n)copy(response, buf[0:n])_, err = conn.WriteToUDP(response, addr) // Send data.if err != nil {fmt.Println("Write to udp failed, err: ", err)}}func main() {localAddr, _ := net.ResolveUDPAddr("udp", ":6666") // Create a UDP address using the local address and port.conn, err := net.ListenUDP("udp", localAddr) // Create a listener.if err != nil {panic("Failed to listen for UDP connections:" + err.Error())}defer conn.Close() // Close the connection at the end.for {handleConn(conn) // Handle the incoming connection.}}
#include <stdio.h>#include <stdlib.h>#include <string.h>#include <arpa/inet.h>#include <netinet/in.h>#include <sys/socket.h>#define BUF_SIZE 1024struct NetworkConnection {uint16_t magic;struct in6_addr clientAddr;struct in6_addr proxyAddr;uint16_t clientPort;uint16_t proxyPort;};void handleConn(int sockfd) {struct sockaddr_in clientAddr;socklen_t addrLen = sizeof(clientAddr);unsigned char buf[BUF_SIZE];ssize_t n = recvfrom(sockfd, buf, BUF_SIZE, 0, (struct sockaddr *)&clientAddr, &addrLen);if (n < 0) {perror("Error reading from UDP connection");return;}// Convert the received bytes to a NetworkConnection struct.struct NetworkConnection nc;nc.magic = ntohs(*(uint16_t *)buf);if (nc.magic == 0x56EC) { // Magic with the value 0x56EC indicates an SPP header.memcpy(&nc.clientAddr, buf + 2, 16);memcpy(&nc.proxyAddr, buf + 18, 16);nc.clientPort = ntohs(*(uint16_t *)(buf + 34));nc.proxyPort = ntohs(*(uint16_t *)(buf + 36));printf("Received packet:\\n");printf("\\tmagic: %x\\n", nc.magic);char clientIp[INET6_ADDRSTRLEN];char proxyIp[INET6_ADDRSTRLEN];inet_ntop(AF_INET6, &nc.clientAddr, clientIp, INET6_ADDRSTRLEN);inet_ntop(AF_INET6, &nc.proxyAddr, proxyIp, INET6_ADDRSTRLEN);// Print the SPP header information, including magic, real client IP and port, as well as proxy IP and port.printf("\\tclient address: %s\\n", clientIp);printf("\\tproxy address: %s\\n", proxyIp);printf("\\tclient port: %d\\n", nc.clientPort);printf("\\tproxy port: %d\\n", nc.proxyPort);// Print the actual and effective payload.printf("\\tdata: %.*s\\n\\tcount: %zd\\n", (int)(n - 38), buf + 38, n);} else {printf("\\tdata: %.*s\\n\\tcount: %zd\\n", (int)n, buf, n);}// Respond with a packet. Note: The 38-byte SPP header must be returned completely.sendto(sockfd, buf, n, 0, (struct sockaddr *)&clientAddr, addrLen);}int main() {int sockfd = socket(AF_INET, SOCK_DGRAM, 0);if (sockfd < 0) {perror("Failed to create socket");exit(EXIT_FAILURE);}// Create a UDP address using the local address and port.struct sockaddr_in serverAddr;serverAddr.sin_family = AF_INET;serverAddr.sin_addr.s_addr = INADDR_ANY;serverAddr.sin_port = htons(6666);if (bind(sockfd, (struct sockaddr *)&serverAddr, sizeof(serverAddr)) < 0) {perror("Failed to bind");exit(EXIT_FAILURE);}while (1) {handleConn(sockfd);}}
echo "Hello Server" | nc -w 1 -u <IP/DOMAIN> <PORT>
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback