Release Notes
Security Announcement
Announcements
http://Hostname/Filename?token=timestamp-rand-uid-md5hashhttps://Hostname/Filename?token=timestamp-rand-uid-md5hash
Field | Description |
Hostname | Site Acceleration Domain. |
Path | Resource access path, authentication requires prefixing with /. |
token | Authentication parameters name set by Definition. |
timestamp | Decimal positive integer Unix timestamp (the total number of seconds from 00:00:00, January 1, 1970, UTC time, to now, independent of the timezone) |
rand | 0 - 100 characters, a random string consisting of uppercase and lowercase letters and numbers. |
uid | User ID, currently unused, default is 0. |
md5hash | A fixed length string of 32 bits calculated using the MD5 algorithm: Algorithm: MD5(Path-timestamp-rand-uid-key). Authentication Logic: If the request has not expired, the node compares this string value with the md5hash value carried in the request URL. If the values are the same, authentication passes, and the request is responded to; if the values are different, authentication fails, returning 403. |
https://www.example.com/foo.jpg uses Authentication Method A, configured as follows: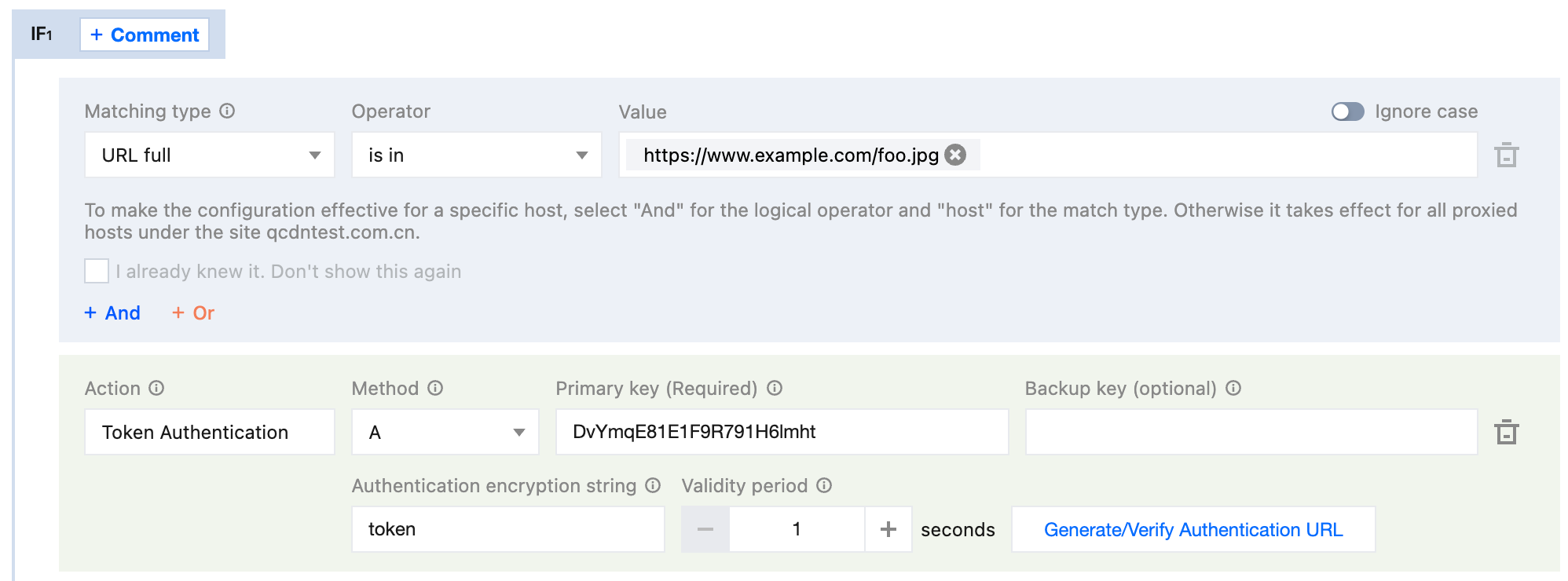
/foo.jpg.1721028437.Kv4cPTAAP5YTi.0.DvYmqE81E1F9R791H6lmht./foo.jpg-1721028437-Kv4cPTAAP5YTi-0-DvYmqE81E1F9R791H6lmht)= 0fbdca749d7ab784750685347e42075c.https://www.example.com/foo.jpg?token=1721028437-Kv4cPTAAP5YTi-0-0fbdca749d7ab784750685347e42075cWas this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback