云产品集成 KMS 实现透明加密
下载
聚焦模式
字号
概述
腾讯云密钥管理系统( Key Management Service,KMS )是一款安全、可靠、简单易用的密钥托管服务,帮助您轻松创建和管理密钥,保护密钥的安全。腾讯云 KMS 可以与大多数腾讯云上的云产品进行无缝集成,在已集成 KMS 的云产品中,仅需要选择一个从 KMS 托管的密钥,即可轻松实现对其云产品内的数据进行加解密。
云产品集成 KMS 加密为您带来如下益处:
云产品通过集成 KMS ,实现对用户数据的加密储存,加密密钥由用户管控。KMS 底层使用 FIPS-140-2 认证的硬件安全模块 HSM 来生成和保护密钥。
为用户提供透明加密的解决方案,用户只需要开通已集成 KMS 的云产品加密服务,无需关心加密的细节,即可实现透明的云上数据加解密。
无需用户自行构建和维护密钥管理基础设施,降低了开发成本,用户使用安全便捷。
说明:
由于其他云产品并不是密钥的托管者,在使用已集成 KMS 的云产品加密数据前,需要通过腾讯云访问管理 CAM ,完成 KMS 对云产品的角色授权操作。
支持的密钥类型
根密钥(Customer Master Key,CMK),是用户或云产品通过密钥管理系统创建的密钥,主要用于加密并保护数据密钥。一个根密钥可以加密多个数据密钥 DEK 。
KMS 提供以下两种根密钥:
自定义密钥
默认的云产品密钥
在用户第一次通过对应云产品使用 KMS 加密时,云产品自动通过密钥管理系统为用户创建的密钥。云产品密钥可通过密钥管理系统控制台进行查询,但不支持禁用、计划删除操作。
加密原理
云产品使用 KMS 加密原理如下图所示:
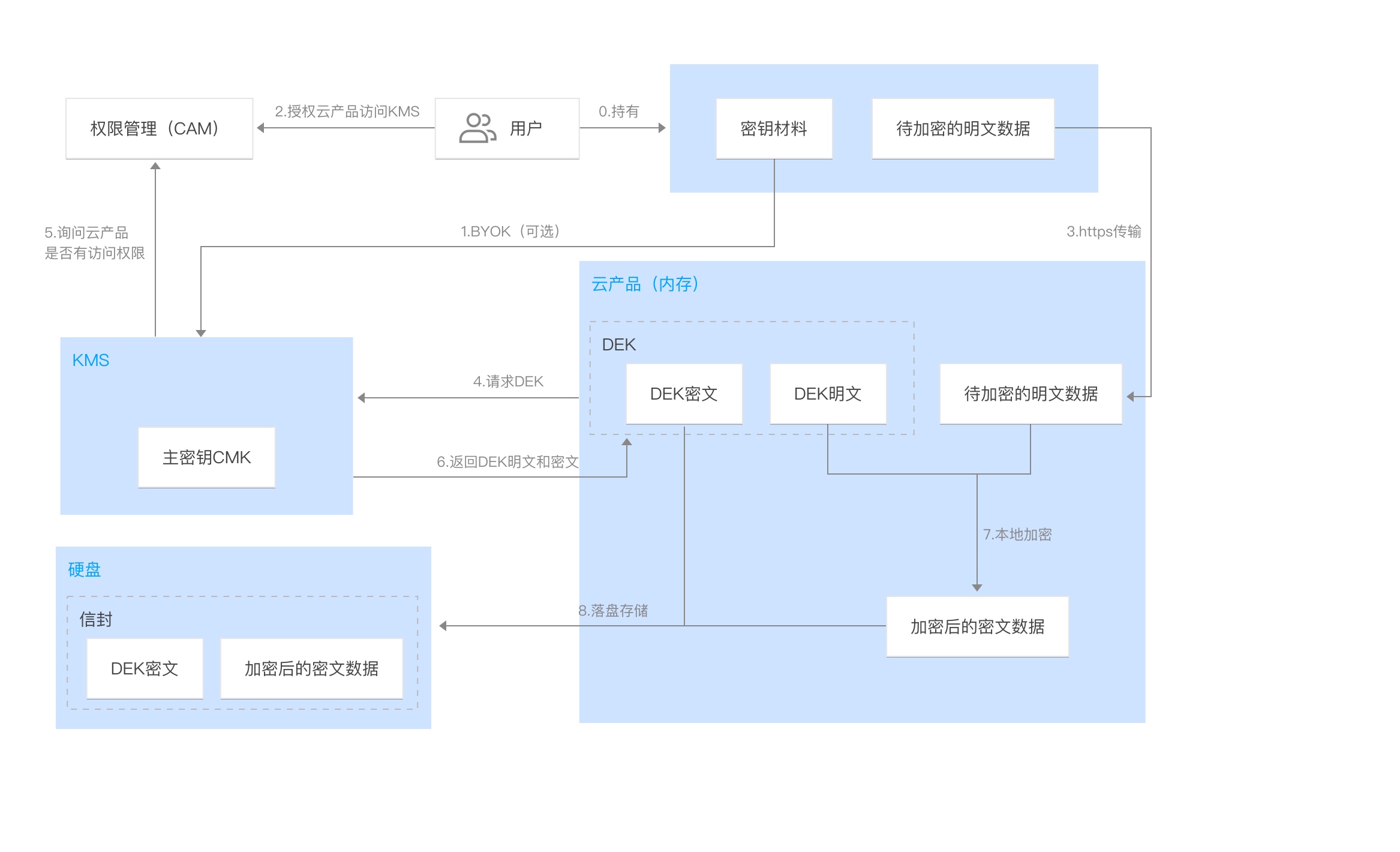
加密流程说明如下:
1. 开通 KMS 服务并且完成 KMS 对云产品的角色授权。
2. 通过 KMS 创建根密钥 CMK,用户可选择默认的云产品密钥或自定义密钥。
3. 通过 CMK 调用 GenerateDataKey 接口生成数据密钥 DEK 密文和 DEK 明文,DEK 受 CMK 加密保护。
4. DEK 明文缓存在云产品后台的内存中,在本地对用户的数据进行加密,得到密文数据。
5. 云产品将 DEK 密文和加密后的密文数据进行落盘储存。
当前支持的云产品
文件存储(Cloud File Storage,CFS)(需开白使用)
文档反馈